What’s new?
- Holistic search across IoCs and adversary intelligence knowledge cards. VirusTotal’s Threat Landscape module incorporates {attribution, threat actor, campaign, toolkit} knowledge cards into our top VirusTotal packages. As of now, whenever you perform free text searches in VirusTotal (e.g. “Emotet”, “Sofacy”, “cve-2017-11882”, “leaked builders”, etc.), the search will be executed not only against the IoC corpus (e.g. antivirus labels for files) but against the full VirusTotal knowledge base including actor/collection knowledge cards, online references and reporting, rules, graph investigations and community comments. The adversary intelligence content appears as a side block on search results listings, clicking on any of its items takes you to the pertinent knowledge card. Note that this functionality is only available to users with access to the Threat Landscape module.

- MITRE ATT&CK TTPs in threat {collection, actor} knowledge cards and open in MITRE ATT&CK Navigator. VirusTotal does not only aggregate detection engines but also dynamic analysis sandboxes. Mandiant CAPA and some of the sandboxes that we aggregate map out execution observations into MITRE ATT&CK tactics and techniques and Malware Behavior Catalog behaviors - see example report. When building threat {collection, actor} cards, VirusTotal aggregates all the mapped TTPs for all the IoCs linked to a given campaign/toolkit/actor and displays them in the TTP tab of the pertinent knowledge card. We’ve now included shortcuts to open these TTP mappings in MITRE ATT&CK Navigator.

- New and enhanced relations in VirusTotal’s underlying threat graph. VirusTotal provides superior context about IoCs. Some of that context is based on relationships with other IoCs and adversary entities, for example: contacted domains, download URLs, resolved IP addresses, compressed bundle parents, execution first stages, etc. We’ve enhanced VirusTotal’s core threat graph as follows:
- Added redirects to relationship. VirusTotal has been displaying target redirection URLs in the Details tab of URL reports for some time now, but this data point has never been added as a full-blown relationship displayed in the Relations tab and explorable via VT Graph. We have now rolled out the “redirects to” relationship.
- Enhanced embedded URLs relationship with memory pattern URLs. VirusTotal extracts URL patterns from the raw binary body of files and builds the embedded URLs relationship with them. This data point is very interesting but also very easy to evade via obfuscation, packing and some other common anti-analysis techniques. To overcome this, as we execute uploaded files in multiple sandboxes, we are now extracting URL patterns from memory and also feeding the embedded URLs relationship with them.

- VirusTotal Connectors. We’ve taken a significant step toward realizing the unified threat contextualization platform with VirusTotal Connectors. All your threat intel from third parties can now be seamlessly merged with VirusTotal's context. When faced with an unfamiliar file, hash, domain, IP address, or URL, having a singular view of threat intelligence not only expedites investigations but also helps eliminate detection blind spots. Learn more.

- File similarity summary view. The concept of similarity is pretty straightforward: are two files similar? There are many ways to figure it out. That's why different similarity algorithms exist. Now, why is this useful? Attackers need tools for their attacks, basically malware. Malware in the end is a piece of software, built from frameworks, code and libraries, and takes some time and expertise to create. The result is that two different malware files built from the same developer using the same pieces or builders will look alike. Tracking similar files often allows you to track actors or campaigns and study them proactively to build effective measures against such threats. VirusTotal has supported a number of file similarity searches for a while now (vhash, behash, imphash, ssdeep, TLSH, icon dhash, etc.). Earlier this year we rolled out some functionality to search across all different similarity approaches available for a file, the “Best candidates in a single search” trigger. Similarity search result listings now display a “Similarity details” toggle to better understand the common data points across matching files.

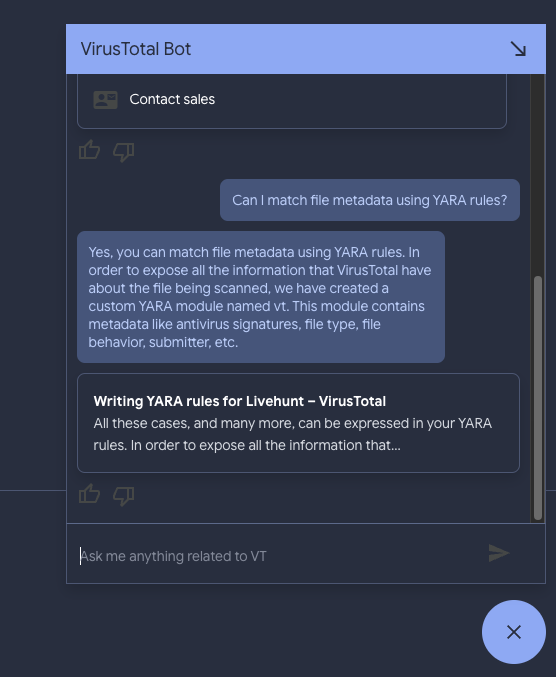
- Documentation chat assistant, a.k.a. VirusTotal bot. At VirusTotal we are committed to democratizing detection engineering and threat hunting. We acknowledge that VirusTotal Enterprise is a sophisticated tool and that not all organizations exhibit the same maturity when it comes to threat intelligence. We are now leveraging generative AI to accelerate our users’ maturity journey. Every single site within VirusTotal displays a small round floating message bubble in the bottom right hand corner. When clicking on it a chat dialog opens up. You can now ask questions (e.g. Can I match file metadata using YARA rules?) related to our documentation and it will summarize docs articles and point you in the right direction.
- Service accounts API documentation. Late last year we rolled out service accounts in order to interact programmatically with VirusTotal leveraging API keys that are not tied to individual users. We have now documented API endpoints related to VirusTotal API service accounts.
What has changed?
- McAfee-Gateway renamed to Skyhigh. Following McAfee Enterprise’s service renaming, the detection engine formerly known as McAfee-Gateway in VirusTotal has been renamed to “Skyhigh”.
What’s new?
- Crowdsourced AI. Mirroring our efforts to improve the industry’s threat visibility via crowdsourcing of antivirus/nextgen/EDR verdicts, dynamic analysis sandbox analyses, crowdsourced {YARA, SIGMA, IDS} rule detections, etc. we are now also bringing together cutting edge AI/ML models from the security community to detect, explain and contextualize threats. Hispasec has been the very first partner joining this effort, their LLM technology produces verdicts and malware analyst copilot explanations around malicious documents, including dissection and code analysis of macros.

- New VT INTELLIGENCE search modifiers. VT INTELLIGENCE is often described as the Google for malware. It allows users to search for IoCs and access superior context to understand threats. It also allows users to perform reverse searches, i.e. to find files, URLs, domains and IPs matching certain criteria. We have added support for the following new modifiers:
- New findings about interesting IoCs via out-of-the-box Livehunt rule templates. VirusTotal {domain, IP address, URL, file} analysis reports now include a new entry in the top header action menu labeled “Follow”. By actioning it you can now create out-of-the-box YARA rules to get notifications on new URLs distributing a given malware sample, new files being downloaded from known malicious infrastructure, new IP address resolutions for a known malicious domain, new subdomains for a given domain, etc. This should ease the task of tracking threat campaigns and democratizes the use of YARA within VirusTotal, beyond advanced binary pattern matching.

- VT HUNTING Livehunt for network indicators. Read launch announcement blog post. VT Hunting Livehunt allows VT Enterprise users to write YARA rules that are matched against the incoming live stream of files uploaded to VirusTotal. It has become a de-facto standard to monitor threat campaigns and malware toolkits, as well as to track threat actors going forward. Livehunt YARA matching in VirusTotal is far richer than standalone, as we allow users to match not only the binary contents of files but also static/dynamic/code analysis properties and other metadata via the “vt” YARA module. We are now extending Livehunt’s matching capabilities to cover domains, IP addresses and URLs. This allows analysts to discover new artifacts and infrastructure tied to a known campaign, unearth new infrastructure being leveraged by popular malware toolkits, perform attack surface management, identify phishing campaigns against their organizations, etc. This is a non-exhaustive list of examples to get you started, we’ve also kicked off a public Github repo to crowdsource rules from the community, Mandiant has been the first contributor, thank you!
- Healthcare industry investigation. We have performed an investigation into the healthcare industry's threat landscape for 2023H1. Most Health Industry targets were victims of ransomware attempts conducted by generic cybercrime gangs. There are few exceptions where Health institutions were targeted as part of cyberespionage actor operations, Yoro Trooper being a notable exception. Check our findings summary.
What’s been fixed?
- When a Retrohunt job is created using the YARA rule editor, the VirusTotal web UI shows a toast with the message “Retrohunt launched! Go”. When the “Go” link is clicked, a new tab with the list of Retrohunt jobs is opened. The new job was shown with the status “0% Starting” indefinitely because its progress was not tracked in the background unless the user reloaded the tab. We have now fixed this to asynchronously retrieve the progress status.